Estimated Read Time – 12–14 minutes
Linux has traditionally been a second‑class citizen in enterprise identity ecosystems. While Windows and macOS benefited from device trust, seamless single sign‑on (SSO), phishing‑resistant MFA, and Conditional Access enforcement, Linux desktops were limited to browser-based authentication and repeated sign‑ins.
That gap is now effectively closed.
Microsoft has made Microsoft Single Sign‑On for Linux generally available, enabling phish‑resistant multifactor authentication (PRMFA) and true device-based trust for Linux desktops through Microsoft Entra ID. This capability is powered by the Microsoft Identity Broker, a native Linux service that integrates authentication, device registration, and compliance into the Entra ecosystem. [learn.microsoft.com]
This article provides a technical deep dive into how it works, why it matters, and how to deploy it securely at scale.
What Is Microsoft Single Sign‑On for Linux?
Microsoft Single Sign‑On (SSO) for Linux is a brokered authentication framework that allows Linux desktops to authenticate once against Microsoft Entra ID and reuse that identity across supported applications and services.
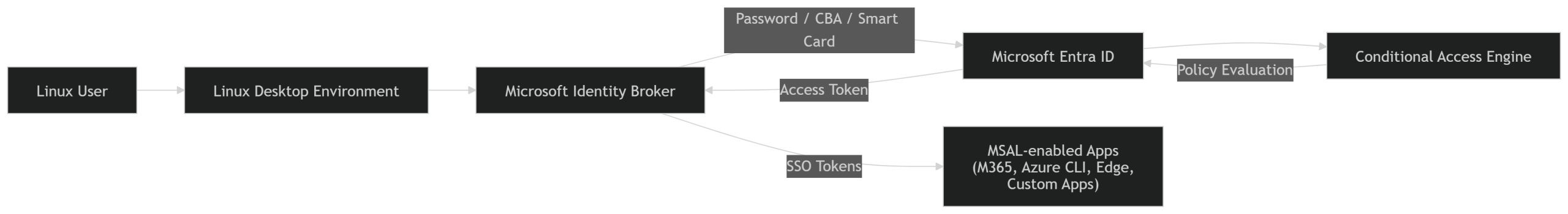
At its core is the Microsoft Identity Broker, a background system service that:
- Handles secure token acquisition
- Manages device identity and registration
- Integrates with Conditional Access
- Enables certificate-based and phishing-resistant authentication
- Provides SSO to apps using Microsoft Authentication Library (MSAL)
This design mirrors the Web Account Manager (WAM) architecture used on Windows and macOS—finally bringing Linux to parity. [learn.microsoft.com]
Why This Matters: Closing a Longstanding Security Gap
1. Phishing‑Resistant MFA on Linux
Linux desktops now support phish‑resistant MFA (PRMFA) through:
- Certificate-Based Authentication (CBA)
- Smart cards and hardware-backed keys (for example, YubiKey with PIV)
Authentication is performed using TLS client certificate validation, where the private key never leaves the hardware or smart card—making credential replay and phishing ineffective. [learn.microsoft.com]
This aligns Linux with modern Zero Trust requirements and NIST AAL3 guidance.
2. True Enterprise SSO Experience
Once authenticated, users gain seamless access to:
- Microsoft 365 web apps
- Azure CLI
- Microsoft Edge (Conditional Access enforced)
- Teams PWA for Linux
- Custom applications using MSAL for Python or .NET
Authentication prompts are brokered and cached securely, eliminating repeated sign-ins and reducing authentication fatigue. [learn.microsoft.com]
3. Linux Can Now Be Entra Joined (Not Just Registered)
Historically, Linux could only be registered to Entra ID. With Microsoft SSO for Linux:
- Devices can be registered and enrolled
- Intune compliance policies apply
- Device-based Conditional Access conditions work
- Access can be blocked based on device trust
This means Linux devices now fully participate in device trust evaluation, a foundational Zero Trust control. [learn.microsoft.com]
4. Simplified Deployment with No Java Dependency
Earlier Linux identity tooling required Java runtimes, complicating deployments and increasing attack surface.
The current Identity Broker implementation removes that dependency entirely, streamlining installation, patching, and security reviews. [learn.microsoft.com]
Supported Platforms
Microsoft currently supports the following Linux distributions for SSO and PRMFA:
- Ubuntu Desktop 22.04 LTS
- Ubuntu Desktop 24.04 LTS
- Red Hat Enterprise Linux 8
- Red Hat Enterprise Linux 9
- Red Hat Enterprise Linux 10 (for smart card scenarios)
These can be physical machines or virtual desktops running on x86_64 hardware. [learn.microsoft.com]
Architecture Overview
High-level flow:
- Microsoft Identity Broker runs as a system service
- User authenticates using password or PRMFA (CBA / smart card)
- Broker acquires Entra ID tokens
- Tokens are securely cached
- MSAL-aware apps request tokens from the broker
- Conditional Access evaluates:
- User identity
- Device trust
- Compliance posture
- Authentication strength
This architecture makes Linux a first-class Zero Trust endpoint.
Enabling Phish‑Resistant MFA (PRMFA)
Beginning with microsoft-identity-broker 2.0.2, Linux supports PRMFA through:
- Smart cards
- USB hardware tokens with PIV/Smartcard applets
- PKI-issued user certificates
Authentication uses TLS mutual authentication, where:
- The device signs a server challenge
- The certificate chain is validated
- Entra ID verifies certificate trust before granting access. [learn.microsoft.com]
Supported Smart Card Scenarios
- YubiKey (PIV)
- PKCS#11-compliant tokens
- OpenSC integrations
Smart card support is available on Ubuntu and RHEL (specific versions). [learn.microsoft.com]
Reference Installation (Ubuntu)
sudo apt install curl gpg
curl https://packages.microsoft.com/keys/microsoft.asc | gpg --dearmor > microsoft.gpg
sudo install -o root -g root -m 644 microsoft.gpg /usr/share/keyrings
sudo apt update
sudo apt install microsoft-identity-broker
sudo rebootOnce installed, device registration and enrollment are initiated via the Identity Broker workflow. [learn.microsoft.com]
Managing Device Registration
Microsoft provides the dsreg utility to manage Linux device identity:
- Unregister device from Entra ID
- Clean broker state
- Remove certificates and keys
Example cleanup:
sudo dsreg --cleanupThis is particularly useful for troubleshooting or re-provisioning devices. [learn.microsoft.com]
Security and Zero Trust Impact
With this release, Linux desktops can now meet the same Zero Trust criteria as Windows and macOS:
| Control | Linux Support |
|---|---|
| Phishing‑resistant MFA | ✅ |
| Device trust | ✅ |
| Conditional Access | ✅ |
| Intune compliance | ✅ |
| Hardware‑backed auth | ✅ |
This dramatically reduces shadow IT, weak authentication exceptions, and Linux-specific policy gaps.
Final Thoughts
Microsoft Single Sign‑On for Linux with phishing‑resistant MFA represents a fundamental shift in enterprise identity strategy.
Linux is no longer a special case—it is now a first-class Zero Trust endpoint.
For organizations supporting mixed-OS environments, this removes the last major identity friction point and delivers consistent security posture across Windows, macOS, and Linux.
Further Reading
- Microsoft Learn: Microsoft Single Sign‑On for Linux [learn.microsoft.com]
- Microsoft Entra Conditional Access documentation
- Intune Linux device management guides